As digital ecosystems grow more complex and surveillance, data restrictions, and cyber threats continue to evolve, proxies have become essential tools for individuals and organizations alike. In 2026, proxy technology is no longer limited to bypassing geo-blocks—it plays a central role in privacy protection, cybersecurity, market research, automation, and performance optimization. Used responsibly, proxies enhance operational efficiency while safeguarding sensitive information in a rapidly changing online landscape.
TL;DR: Proxies in 2026 are essential for maintaining privacy, strengthening cybersecurity, conducting market research, managing multiple accounts, and optimizing network performance. Businesses and individuals rely on residential, datacenter, and mobile proxies for secure and scalable digital operations. When used ethically and in compliance with regulations, proxies provide a powerful layer of protection and strategic advantage. Choosing the right proxy type depends on the specific use case and risk profile.
Understanding Proxies in 2026
A proxy server acts as an intermediary between a user and the internet. Instead of connecting directly to a website, the request passes through a proxy server, which assigns a different IP address and forwards the request. This process can:
- Mask the original user IP address
- Distribute traffic across multiple endpoints
- Filter or monitor outgoing and incoming data
- Improve anonymity and reduce targeting risks
With rising concerns about privacy, AI-driven tracking, and geo-restrictions, proxy networks have become increasingly sophisticated. Today’s solutions integrate encryption, rotation logic, compliance monitoring, and scalable IP pools suitable for enterprise-grade deployment.
1. Privacy and Identity Protection
Online tracking technologies in 2026 use advanced fingerprinting methods, behavioral profiling, and AI-powered analytics. Simply deleting cookies is no longer enough to ensure privacy. Proxies help mitigate these risks by masking IP addresses and reducing traceability.
Primary privacy-driven use cases include:
- Secure browsing on public or shared networks
- Preventing targeted surveillance from data aggregators
- Reducing exposure to identity theft
- Shielding internal company research from competitors
Residential proxies, which route traffic through real residential IPs, are widely used for maintaining high anonymity. For stronger protection, businesses often combine proxies with VPNs and encrypted browsers.
Important note: Privacy-oriented proxy use must comply with local laws and terms of service agreements. Ethical implementation strengthens digital trust rather than undermines it.
2. Cybersecurity and Threat Intelligence
Organizations increasingly deploy proxies as part of broader cybersecurity strategies. By routing security testing traffic through segmented IP pools, businesses can safely monitor threats without exposing core infrastructure.
Common cybersecurity applications include:
- Penetration testing and vulnerability scanning
- Threat intelligence gathering
- Monitoring dark web leak sources
- Fraud detection research
Proxies allow security teams to simulate user behavior from different geographic regions, identifying vulnerabilities that might otherwise remain hidden. In a zero-trust security environment, segmented proxy routing adds another defensive layer.
3. Market Research and Competitive Intelligence
Global markets shift rapidly, and businesses rely on accurate, location-specific data to stay competitive. Proxies enable companies to gather publicly available information without triggering anti-bot systems or geo-restrictions.
Key applications include:
- Localized price monitoring across regions
- Ad verification and campaign auditing
- Search engine results analysis
- Tracking industry trends in real time
Without proxies, automated data collection efforts risk IP bans and incomplete datasets. Rotating proxy pools reduce detection risks while enabling scalable data access.
Businesses must ensure that data collection practices comply with applicable laws such as data protection and fair use regulations.
4. Managing Multiple Accounts and Social Media Automation
Marketing teams, e-commerce operators, and agencies often manage multiple regional accounts across platforms. Most major services limit multiple accounts per IP address, making proxies vital for lawful account separation and operational continuity.
Use cases include:
- Regional social media management
- Global customer support operations
- Marketplace seller account maintenance
- Ad campaign segmentation testing
Mobile proxies are increasingly favored for social engagement tasks because they mirror real-world mobile user behavior. Proper proxy rotation reduces automated detection flags.

5. Accessing Geo-Restricted Content and Services
Content licensing agreements and regional regulations often restrict digital services by location. Proxies help organizations test region-specific user experiences and confirm service functionality across borders.
This is particularly relevant for:
- Streaming service quality testing
- International SaaS deployment
- E-commerce localization validation
- Cross-border financial service verification
For enterprises operating globally, the ability to validate compliance and availability in different jurisdictions is critical.
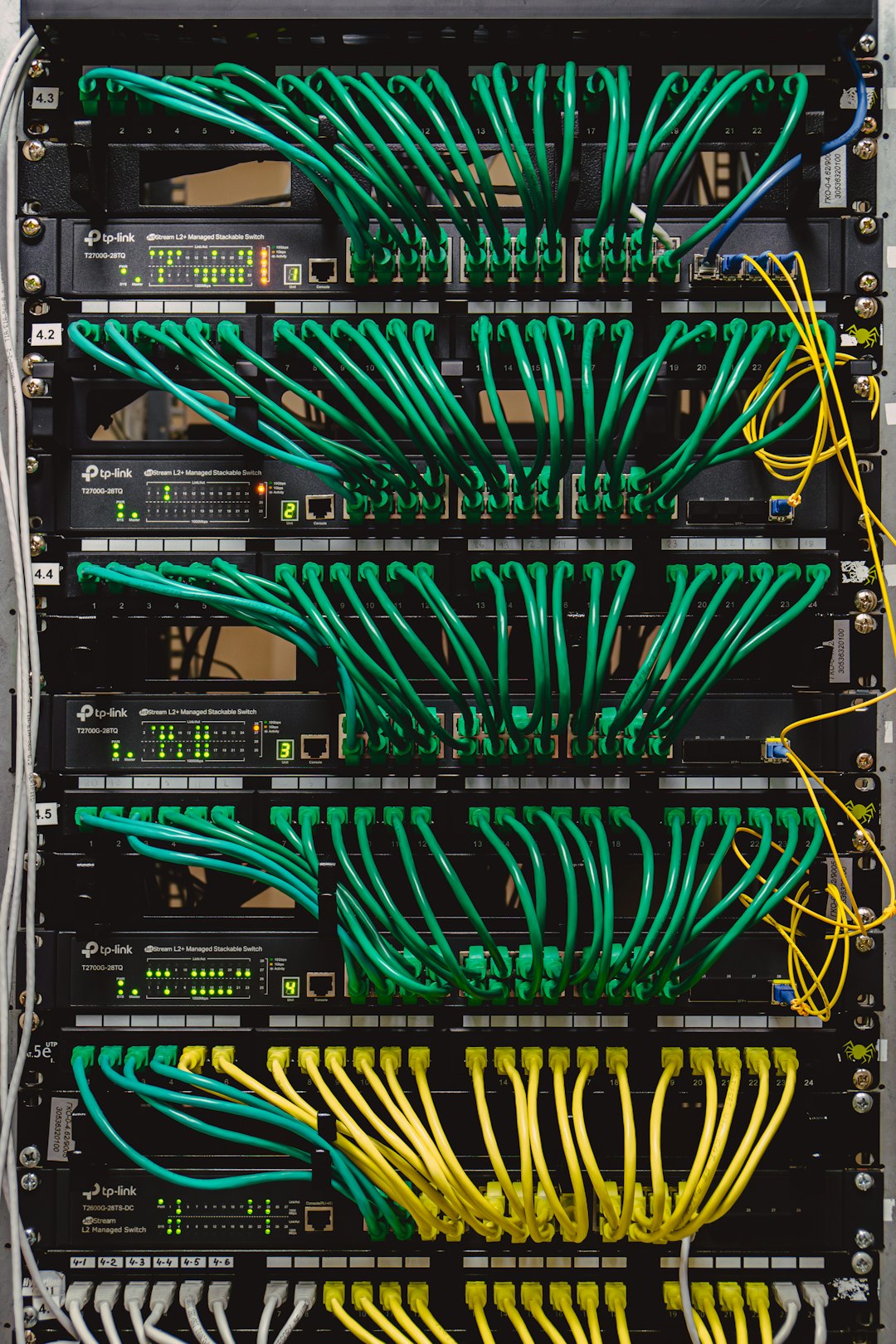
6. Improved Network Performance and Traffic Optimization
Forward and reverse proxy systems are also used to enhance performance and reliability. This use case is often overlooked but remains critical in enterprise architecture.
Benefits include:
- Load balancing across multiple servers
- Bandwidth compression
- Caching frequently accessed resources
- Minimizing latency for distributed teams
Reverse proxies such as Nginx and HAProxy are frequently deployed at the infrastructure level to improve scalability and uptime.
Types of Proxies and Their Best Use Cases
Different proxy types serve different operational goals. The comparison below outlines their primary strengths.
| Proxy Type | Best For | Strengths | Limitations |
|---|---|---|---|
| Residential | High-anonymity browsing, market research | Harder to detect, large geographic diversity | Higher cost |
| Datacenter | High-speed automation, server tasks | Fast and scalable | More detectable |
| Mobile | Social media management, ad verification | Authentic mobile IP behavior | Limited availability, premium pricing |
| Reverse Proxy | Infrastructure optimization | Load balancing and security | Requires server configuration expertise |
Compliance and Ethical Considerations in 2026
Proxy use carries responsibility. Governments and regulatory bodies are increasingly focused on transparency, privacy rights, and cybersecurity compliance. Businesses should:
- Verify data collection complies with privacy regulations
- Respect platform terms of service
- Maintain internal audit trails
- Implement role-based access controls
- Conduct regular proxy provider assessments
Reputable proxy providers now offer compliance documentation, consent-based residential networks, and monitoring tools to prevent misuse.
Choosing the Right Proxy Provider
When selecting a provider in 2026, decision-makers should evaluate:
- IP pool size and diversity
- Uptime guarantees
- Rotation capabilities
- Encryption and authentication features
- Transparent sourcing practices
- Customer and technical support quality
Cost alone should never determine selection. Reliability, compliance assurances, and long-term scalability matter more than short-term savings.
Looking Ahead
As artificial intelligence enhances tracking capabilities and cybersecurity risks intensify, proxies will remain indispensable tools for maintaining digital control. Their evolution in 2026 reflects broader shifts toward privacy awareness, distributed infrastructure, and regulatory accountability.
Whether used for privacy protection, security research, competitive intelligence, or infrastructure optimization, proxies provide a flexible and powerful solution when implemented responsibly. Organizations that treat proxy deployment as a strategic investment—rather than a workaround—will be better positioned to navigate the complexities of the modern digital environment.
In a landscape defined by constant change, the ability to stay private, smart, and secure is not optional—it is foundational. Proxies, when chosen correctly and deployed ethically, are central to achieving that objective.